What is an image?
Images come in a variety of types. We have photographs, which are images. Computer images are very similar. Both are copies of things from a single point in time. We will be working with a copy of a computer that has been acting weird. Don’t worry though, this won’t hurt your computer! Remember that the OS will be in a sandbox, meaning that it can’t affect your computer.
Setting up Kali Linux
Downloading the image
OS images make it easy to send exact copies of computers.
VirtualBox uses the .ova file extension for their machine images. This is similar to how you save documents as a .docx file and photographs as .png.
Let’s download our copy of the computer! Click the link below to download.
Most OS images are big (~8GB), but ours is only ~3GB. The download may still take a few minutes.
Importing the Virtual Machine
Now that you have the machine image downloaded, it is time to set it up!
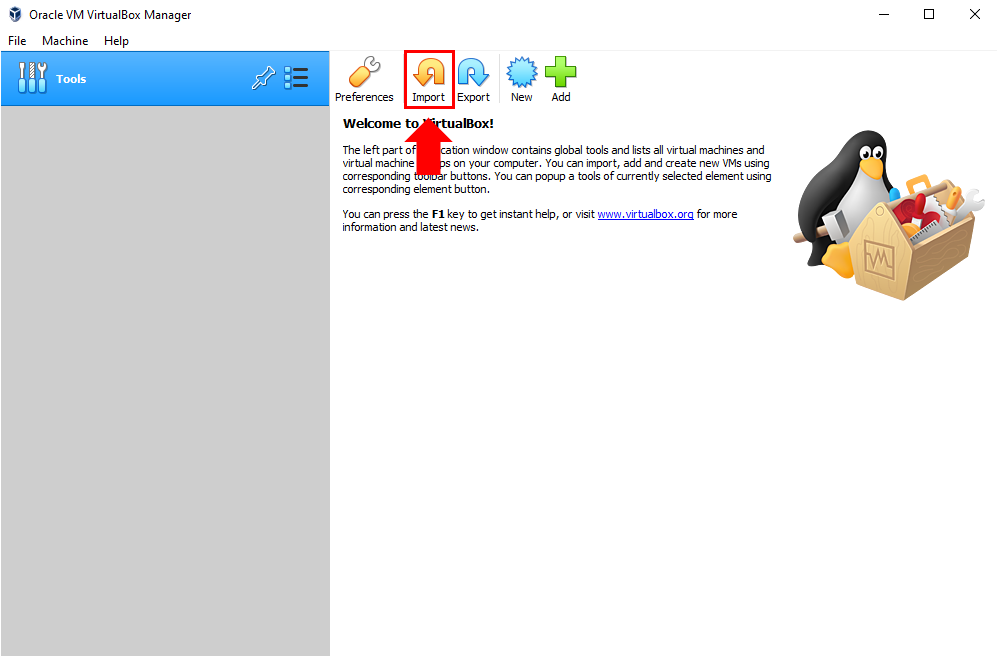
Step 1
In the VirtualBox application, we are able to import our images. Let’s click on the “Import” button to get started!
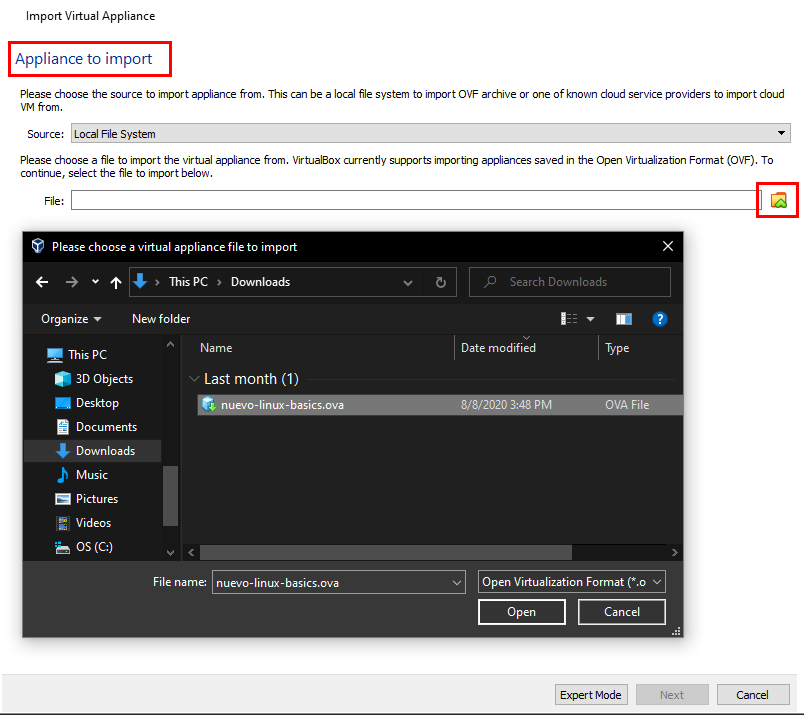
Step 2
The appliance we want to import will be the .ova file you downloaded earlier. Go ahead and click on the little folder with a green caret symbol. This will open up a window so you can find and select the .ova file.
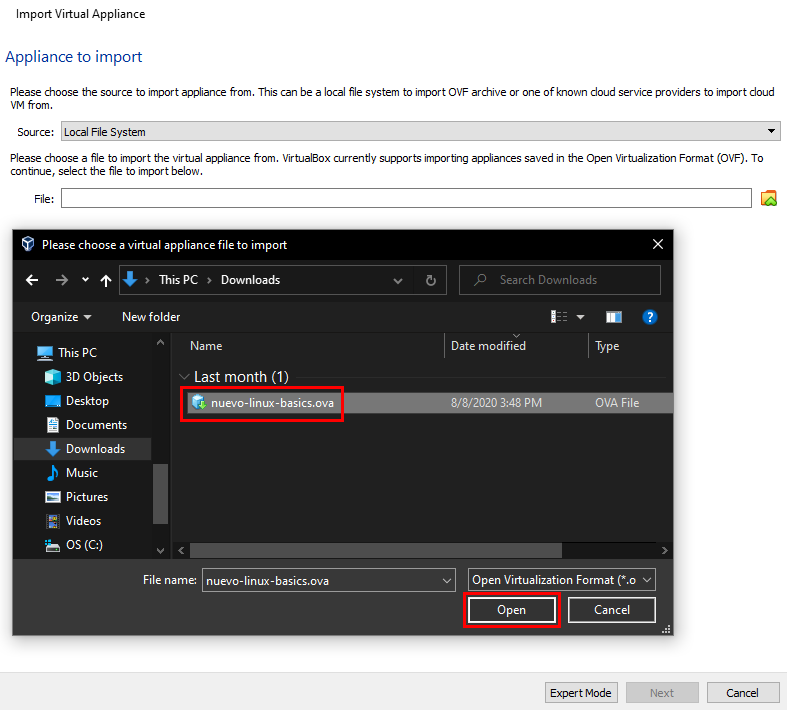
Step 3
Now that you selected the .ova image file. Click “Open”. Then click “Next” on the “Appliance to Import” screen.
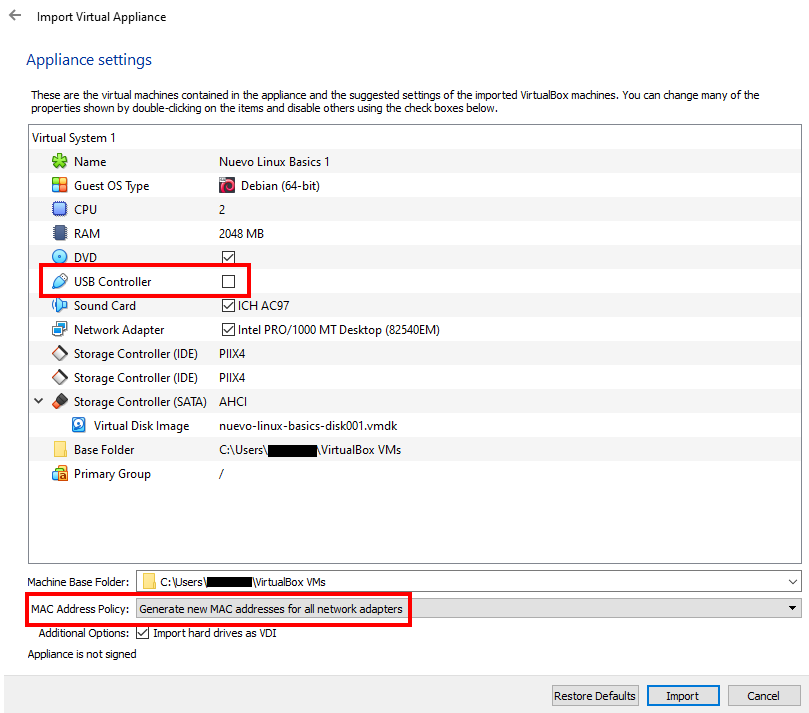
Step 4
The last step! In the “Name” field, feel free to give it a new name. It’s your own VM! Make sure that the “USB Controller” option is not selected. Make sure to uncheck it. Next, for the MAC Address Policy, it is a good idea to make sure that it says, “Generate new MAC addresses for all network adapters”. Finally, click “Import”!
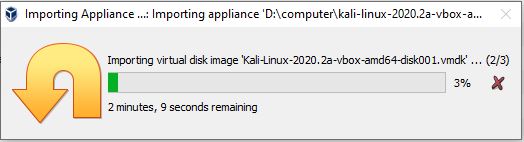
Note: this will have a pop-up with the time needed to complete the import.
Typically this is about 5 minutes, but it might take a little longer depending on your computer.